[ad_1]
A hacking group identified with the name of “Worok” has devised a technique for hide malware within PNG images so that a system can be compromised without triggering any alarms. The discovery was made by Avast security researchers, thanks to previous work by ESET which first identified Worok’s business in early September.
During ESET’s investigations, it emerged that Worok targeted high-profile targets, including government realities in the Middle East, Southeast Asia and South Africa. At the time of ESET’s analysis, however, it had been difficult to shed light on the attack methods and techniques of the hacker group.
Starting from the elements that emerged during the analysis of ESET, Avast continued the work and managed to confirm what was previously hypothesized, namely the use of PNG images as an attack vector. Currently, the method Worok uses to breach network security remains unknown, but Avast believes there is a high likelihood of using DDL sideloading techniques to execute CRLLoader.
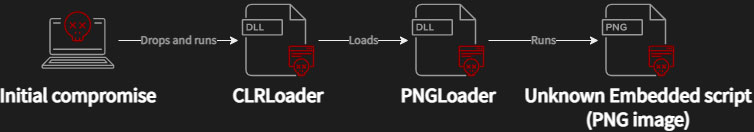
Once the attackers have managed to breach the network, a second DLL, PNGLoader, is loaded through CRLLoader, which will have the task of extracting the information hidden in the PNG files and assembling them to build two executables.
Malicious code is hidden inside PNG files using steganography, so that images appear as such when viewed with ordinary tools. In the particular case of the Worok malware, the technique used is called Least Significant Bit Encoding and it is based on the insertion of small code fragments in the less important bits of the image pixels.
Once the code has been extracted and assembled, on the targeted machine there are executables that allow you to steal information and send it in the form of an archive in a Dropbox account controlled by Worok.
Avast notes that the tools that were observed during the analyzes are not freely available on the network, and are therefore likely for the exclusive use of Worok.
.
[ad_2]
Source link
